Audit Log Process
Certain user operations have the potential to result in serious security incidents or financial losses. Audit logs, which record the execution of such operations, can be used as legal grounds and audit trails.
Audit logs are required to be stored for a longer period, typically five years or more, compared to general operation logs.
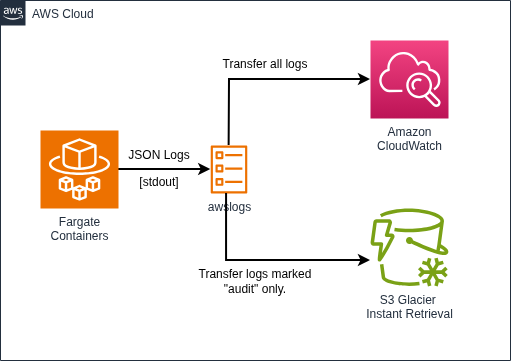
The following is an example of a standard configuration for storing audit logs at low cost in an AWS environment.
Processing Flow
- Each program within the container labels the audit log to indicate that it is an audit log (for example, storing the value "audit" in the category field of the structured log).
- Each program encodes the event log, including the audit log, in JSON format and outputs it to standard output.
- Using the AWS awslogs driver, the destination is determined by examining the value of the category field in the output log. All logs are transferred to the AWS CloudWatch service, and audit logs are also stored in S3 Glacier storage.
- S3 Glacier storage is designed for long-term storage and allows for inexpensive long-term data storage.
- If you need to improve the reliability of audit logs, you should enable object lock setting of S3.